How Linux works
Have you ever wondered what exactly DCOP is, or where your drivers are hidden?
Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
The main problem you face when you're attempting to lift the lid on what makes Linux tick is knowing where to start. It's a complicated stack of software that's been developed by thousands of people.
Following the boot sequence would be a reasonable approach, explaining what Grub actually does, before jumping into the initiation of a RAM disk and the loading of the kernel. But the problem with this is obvious. Mention Grub too early in any article and you're likely to scare many readers away. We'd have the same problem explaining the kernel if we took a chronological approach.
Instead, we've opted for a top-down view, tackling each stratum of Linux technology from the desktop to the kernel as it appears to the average user. This way, you can descend from your desktop comfort zone into the underworld of Linux archaeology, where we'll find plenty of relics from the bygone era of multi-user systems, dumb terminals, remote connections and geeks gone by.
Article continues belowThis is one of the things that makes Linux so interesting: you can see exactly what has happened, why and when. This enables us to dissect the operating system in a way we couldn't attempt with some alternatives, while at the same time, you learn something about why things work the way they do on the surface.
Level 1: Userspace
Before we delve into the Linux underworld, there's one idea that's important to understand. It's a concept that links userspace, privileges and groups, and it governs how the whole Linux system works and how you, as a user, interact with it.
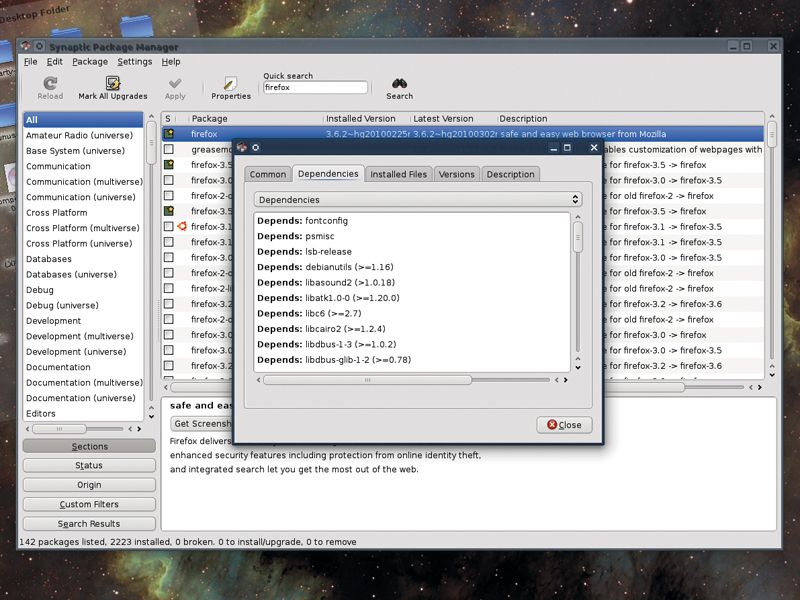
It's based on the premise that a normal desktop user shouldn't be able to make important system changes without proving that they have the correct administrator's privileges to do so. This is why you're asked for a password when you install new packages or open your distribution's configuration panels, and it's why a normal user can't see the contents of the /root directory or make changes to specific files.
Sign up for breaking news, reviews, opinion, top tech deals, and more.
Your distribution will use either sudo or an administrator account to grant access to the system-wide configurable parts of your system. The former will work typically only for a single session or command, and is used as an ad-hoc solution for normal day-to-day use, much like the way both Windows 7 and OS X handle privileges.
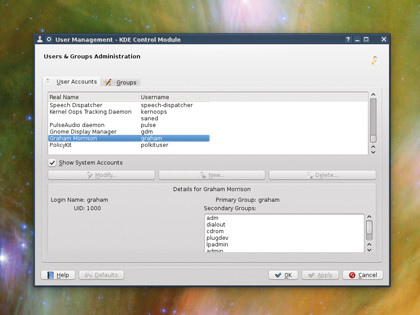
USER CONTROL: Groups make it possible to enable and disable certain services on a per-user basis
With a full-blown system administrator's account, on the other hand, it's sometimes far too easy to stay logged in for too long (and thus more likely that you'll make an irreversible mistake or change). But the reason for both methods is security.
Linux uses a system of users, groups and privilege to keep your system as secure as possible. The idea is that you can mess around with your own files as much as you like, but you can't mess about with the integrity of the whole system without at least entering a password. It might seem slightly redundant on a system when you are the only user of your system, but as we'll see with many other parts of Linux, this concept is a throwback to a time when the average system had many users and only a single administrator or two.
Linux is a variant of the Unix operating system, which has been one of the most common multi-user systems for decades. This means that multi-user functionality is difficult to avoid in Linux, but it's also one of the reasons why Linux is so popular – multi-user systems have to be secure, and Linux has inherited many of the advantages of these early systems.
A user account on Linux is still self-contained, for example. All of your personal files are held within your own home directory, and it's the same for other users of the system. You can usually see their names by looking at the contents of /home with your file manager, and depending on their permissions, even look inside other people's home folders.
But who can and can't read their contents is governed by the user who owns the files, and that's down to permissions.
Permissions
Every file and directory on the Linux filesystem has nine attributes that are used to define how they can be accessed. These attributes correspond to whether a user, a group or anyone can read, write and execute the file.
You might want to share a collection of photos with other users of your system, for example, and if you create a group called 'photos', add all the users who you'd like access to the group and set the group permissions for the photos folder, you'll be able to limit who has access to your images.
Any modern file manager will be able to perform this task, usually by selecting a file and choosing its properties to change its permissions. This is also how your desktop will store configuration information for your applications, tools and utilities.
Hidden directories (those that start with a full stop), are often created within your home directory, and within these you'll find text files that your desktop and applications will use to store your setup.
No one else can see them, and it's one of the reasons why porting your current home directory to a new distribution can be such a good idea – you'll keep all your settings, despite the entire operating system changing.