This infostealer has a vicious sting for Python developers
Malicious packages are targeting Python devs again
Cybersecurity researchers from Checkmarx have discovered more than two dozen malicious packages on PyPI, a popular repository for Python developers, and released their findings in a new report.
These malicious packages, designed to look almost identical to legitimate ones, try to trick reckless developers into downloading and installing the wrong one, thus distributing malware.
The practice is known as typosquatting and it’s quite popular among cybercriminals that attack software developers.
Infostealer thefts
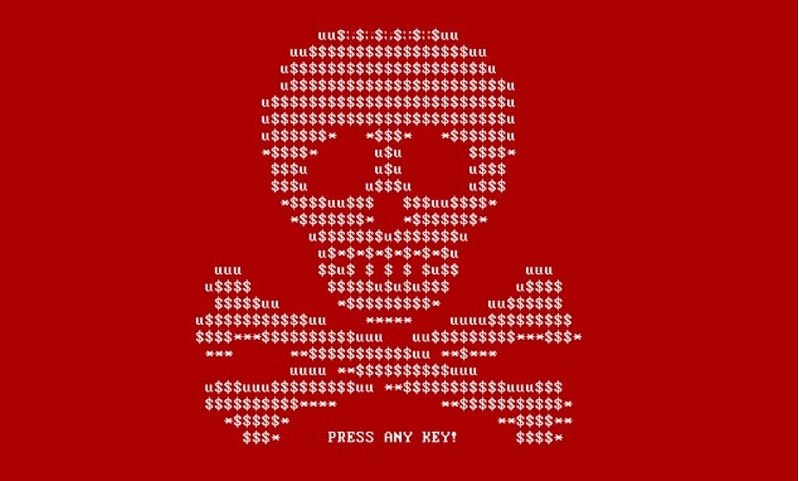
To hide the malware, the attackers are using two unique approaches: steganography, and polymorphism.
Steganography is the practice of hiding code inside an image, which allows threat actors to distribute malicious code through seemingly innocent .JPGs and .PNGs.
Polymorphic malware, on the other hand, changes the payload with every install, thus successfully avoiding antivirus programs and other cybersecurity solutions.
Here, the attackers used these techniques to deliver WASP, an infostealer capable of grabbing people’s Discord accounts, passwords, cryptocurrency wallet information, credit card data, as well as any other information on the victim’s endpoint deems interesting.
Are you a pro? Subscribe to our newsletter
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
Once identified, the data is sent back to the attackers via a hard-coded Discord webhook address.
The campaign seems to be a marketing stunt, as apparently the researchers spotted the threat actors advertising the tool on the dark web for $20 and claiming that it's undetectable.
Furthermore, the researchers believe this to be the same group that was behind a similar attack that was first reported earlier this month by researchers at Phylum and Check Point. Back then, it was said that a group dubbed Worok was distributing DropBoxControl, a custom .NET C# infostealer that abuses Dropbox file hosting for communication and data theft, since at least September 2022.
Given its toolkit, the researchers believe Worok to be the work of a cyberespionage group that works quietly, likes to move laterally across target networks, and steal sensitive data. It also seems to be using its own, proprietary tools, as the researchers haven’t observed them being used by anyone else.
- Check out the best firewalls around
Via: The Register
Sead is a seasoned freelance journalist based in Sarajevo, Bosnia and Herzegovina. He writes about IT (cloud, IoT, 5G, VPN) and cybersecurity (ransomware, data breaches, laws and regulations). In his career, spanning more than a decade, he’s written for numerous media outlets, including Al Jazeera Balkans. He’s also held several modules on content writing for Represent Communications.