This odd malware tricks Google to boost your website's SEO - then it attacks
Researchers say Gootkit is being used to deliver all kinds of malware, trojans, and ransomware

Security researchers have discovered a novel malware delivery mechanism that climbs to the top of any search results after tricking Google’s famed SEO (Search Engine Optimization) algorithm.
While the Gootkit malware itself has been around for several years, and has been analyzed by cybersecurity firm Sophos in the past, it is its new delivery mechanism, which has earned it the nickname Gootloader and is the subject of their recent analysis.
“Gootloader uses malicious search engine optimization (SEO) techniques to squirm into Google search results. The way it accomplishes this task deserves some discussion, because it centers as much around technology as human psychology,” shares Sophos.
- Keep your devices virus-free with the best malware removal software
- Here’s a list of the best website defacement monitoring services
- We've put together a list of the best endpoint protection software
Search engine deoptimization
In their breakdown of the delivery mechanism, the researchers estimate that the operators of the malware run a network of about 400 servers that serve hacked versions of legitimate websites.
To illustrate the effectiveness of this method, the researchers published screenshots that show Google returning one of the websites run by the malware operators as the first result. Even more impressive is the fact that the hacked website belonged to a neonatal clinic while the search query centered on real estate.
When clicked, the hacked website will appear to legitimately provide an answer to the search query, which will involve downloading a zip file, which obviously contains the malware.
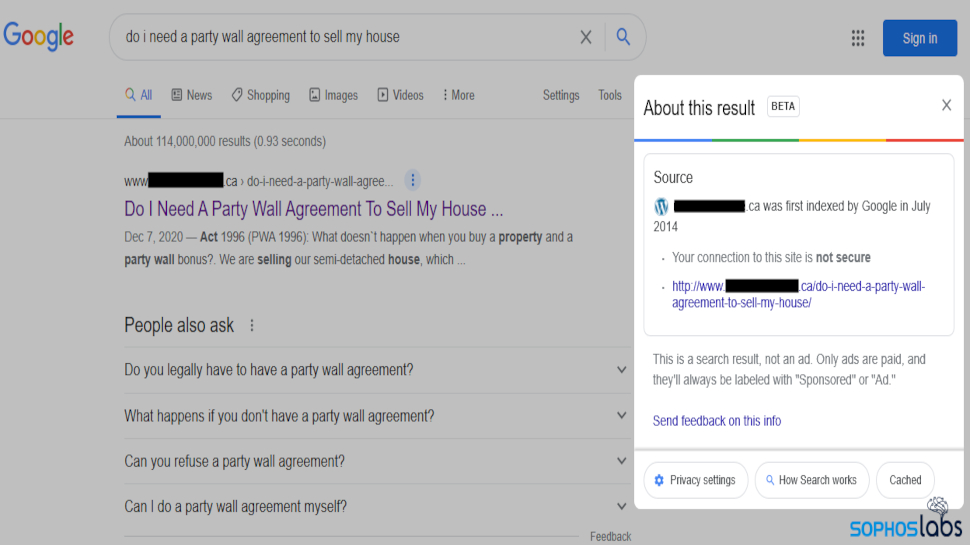
The researchers share that as per their analysis, many of the hacked websites were running well-known content management systems (CMS), without naming them. The threat actors have tweaked the backend that fetches and runs a script to make the websites present a slightly modified version of the original information based on the victim’s search query.
Are you a pro? Subscribe to our newsletter
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
The researchers note that this new mechanism is being used to not just spread Gootkit, but several other trojans and ransomware such as Kronos, REvil, Cobalt Strike, and more.
Sophos claims that it is the layers of tricks that makes this delivery mechanism so effective. “At several points, it’s possible for end users to avoid the infection, if they recognize the signs. The problem is that even trained people can easily be fooled by the chain of social engineering tricks Gootloader’s creators use,” believe the researchers.
- We've also highlighted the best antivirus around today
Via ZDNet
With almost two decades of writing and reporting on Linux, Mayank Sharma would like everyone to think he’s TechRadar Pro’s expert on the topic. Of course, he’s just as interested in other computing topics, particularly cybersecurity, cloud, containers, and coding.
