Critical server-side vulnerability in Microsoft Copilot Studio gives illegal access to internal infrastructure
Bad handling of redirect status codes allows hackers to manipulate HTTP requests
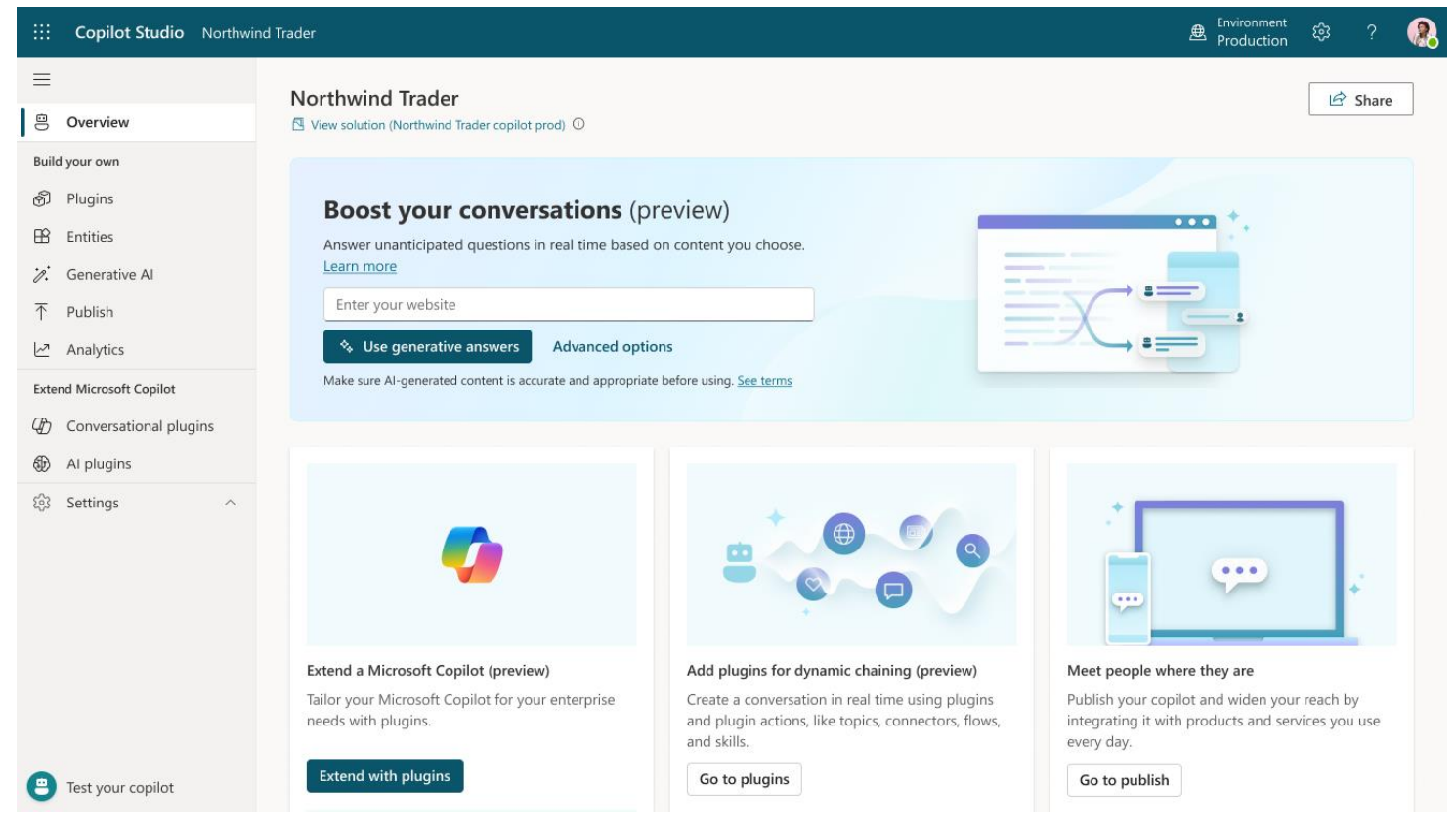
A critical vulnerability has been discovered in Microsoft’s Copilot Studio, posing significant risks to sensitive internal data. This flaw, identified as a server-side request forgery (SSRF), allows unauthorized access to internal infrastructure, potentially impacting multiple tenants.
The flaw identified by Tenable's Research Team is attributed to improper handling of redirect status codes in user-configurable actions, which allows attackers to manipulate HTTP requests.
This vulnerability is tracked as CVE-2024-38206 and has a CVSS score of 8.5, indicating its critical severity level. Microsoft has confirmed that this issue has been tackled as of July 31, 2024, and users do not need to take any further action.
Server-Side Request Forgery (SSRF) could have broader implications
The SSRF vulnerability identified in Copilot Studio stems from the manipulation of an application to make server-side HTTP requests to unintended targets or locations. This manipulation can lead to unauthorized access to internal resources that are typically protected. Essentially, an attacker could exploit this flaw to make requests on behalf of the application to sensitive internal resources, revealing potentially sensitive data.
In the case of Copilot Studio, the SSRF vulnerability could have been exploited to access Microsoft’s Instance Metadata Service (IMDS). The IMDS is a common target for SSRF attacks in cloud environments because it can yield information such as managed identity access tokens. These tokens can then be used to gain further access to shared resources within the environment, including databases.
For instance, gaining access to a Cosmos DB, where sensitive data is stored, could compromise data integrity and confidentiality, leading to broader security breaches and potential data leaks affecting multiple customers.
This discovery is not an isolated incident. It follows Tenable's previous findings of vulnerabilities in various Microsoft services, including the Azure Health Bot service, Azure Service Tags, and multiple vulnerabilities within the Azure API Management service. The pattern indicates a concerning trend in the security posture of Microsoft’s cloud offerings, particularly as they expand rapidly in a competitive market.
Are you a pro? Subscribe to our newsletter
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
“In the context of cloud applications, a common target is the Instance Metadata Service (IMDS) which, depending on the cloud platform, can yield useful, potentially sensitive information for an attacker. In this case, we were able to retrieve managed identity access tokens from the IMDS. No information beyond the usage of Copilot Studio was required to exploit this flaw,” explains Jimi Sebree, senior staff research engineer, at Tenable.
“As in some of the previous vulnerabilities found by our research team, this vulnerability demonstrates that mistakes can be made when companies rush to be the first to release products in a new or rapidly expanding space,” Sebree concluded.
More from TechRadar Pro
- These are the best AI tools and best AI writers
- This sophisticated new phishing campaign is going after US government contractors
- Take a look at our pick of the best firewalls

Efosa has been writing about technology for over 7 years, initially driven by curiosity but now fueled by a strong passion for the field. He holds both a Master's and a PhD in sciences, which provided him with a solid foundation in analytical thinking. Efosa developed a keen interest in technology policy, specifically exploring the intersection of privacy, security, and politics. His research delves into how technological advancements influence regulatory frameworks and societal norms, particularly concerning data protection and cybersecurity. Upon joining TechRadar Pro, in addition to privacy and technology policy, he is also focused on B2B security products. Efosa can be contacted at this email: udinmwenefosa@gmail.com