Ghost ransomware has hit firms in over 70 countries, FBI and CISA warn
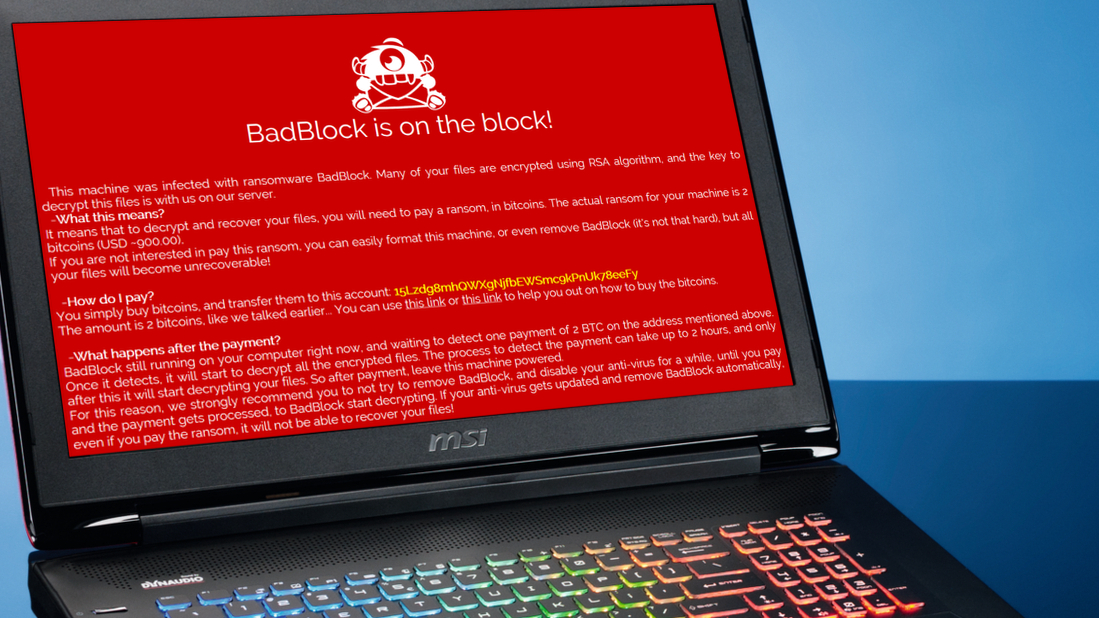
Ransomware groups were often changing names and encryptors
- FBI and CISA have warned about Ghost ransomware operators
- The threat actors are hitting critical infrastructure, government, and other organizations
- They are breaching networks through unpatched, vulnerable endpoints
Cybercriminal groups using the Ghost ransomware variant have so far successfully breached organizations in more than 70 countries around the world, experts have claimed.
A new joint security advisory, recently published by the US Cybersecurity and Infrastructure Security Agency (CISA), the FBI, and the Multi-State Information Sharing and Analysis Center (MS-ISAC) noted the groups are mostly targeting critical infrastructure organizations, but are also interested in healthcare, government, technology, manufacturing, and other verticals. The victim organizations can be both large enterprises and small- or medium-sized businesses (SMB).
"Beginning early 2021, Ghost actors began attacking victims whose internet-facing services ran outdated versions of software and firmware," the three agencies said in the report. "This indiscriminate targeting of networks containing vulnerabilities has led to the compromise of organizations across more than 70 countries, including organizations in China."
Different names
Since the groups use different names, different file extensions, different ransom notes, and more, attribution was relatively difficult, it was further explained. Apparently, they used multiple names, including Ghost, Cring, Crypt3r, Phantom, Strike, Hello, Wickrme, HsHarada, and Rapture. For encryptors, the researchers observed Cring.exe, Ghost.exe, ElysiumO.exe, and Locker.exe.
To compromise their victims, the groups went for unpatched endpoints. Most of the time, they were targeting Fortinet (CVE-2018-13379), ColdFusion (CVE-2010-2861, CVE-2009-3960), and Exchange (CVE-2021-34473, CVE-2021-34523, CVE-2021-31207) flaws.
The best way to defend against Ghost ransomware operators is to keep your software and hardware up to date. All of the vulnerabilities listed in the report have already been fixed by their respective vendors, so mitigating the risk is as easy as applying a patch.
Besides the above-mentioned flaws, state-sponsored hackers were also targeting CVE-2018-13379 to, among other things, breach internet-connected US election support systems. This bug was patched years ago, with Fortinet warning about its abuse on numerous occasions throughout 2019, 2020, and 2021.
Are you a pro? Subscribe to our newsletter
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
Via BleepingComputer
You might also like
- Ransomware attacks surged in 2024 as hackers looked to strike faster than ever
- We've rounded up the best password managers
- Take a look at our guide to the best authenticator app
Sead is a seasoned freelance journalist based in Sarajevo, Bosnia and Herzegovina. He writes about IT (cloud, IoT, 5G, VPN) and cybersecurity (ransomware, data breaches, laws and regulations). In his career, spanning more than a decade, he’s written for numerous media outlets, including Al Jazeera Balkans. He’s also held several modules on content writing for Represent Communications.
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.