More than 70,000 US Army files were exposed ‘for over a year’ even after CISA warning – sensitive personnel info and base schematics stored in vulnerable Open Directory Listing
A leaky database has been found containing sensitive military info
- A leaky directory containing US military data was found in 2024
- Cybernews received a tipoff about the directory and launched an investigation
- The leaky directory remained accessible despite CISA being notified
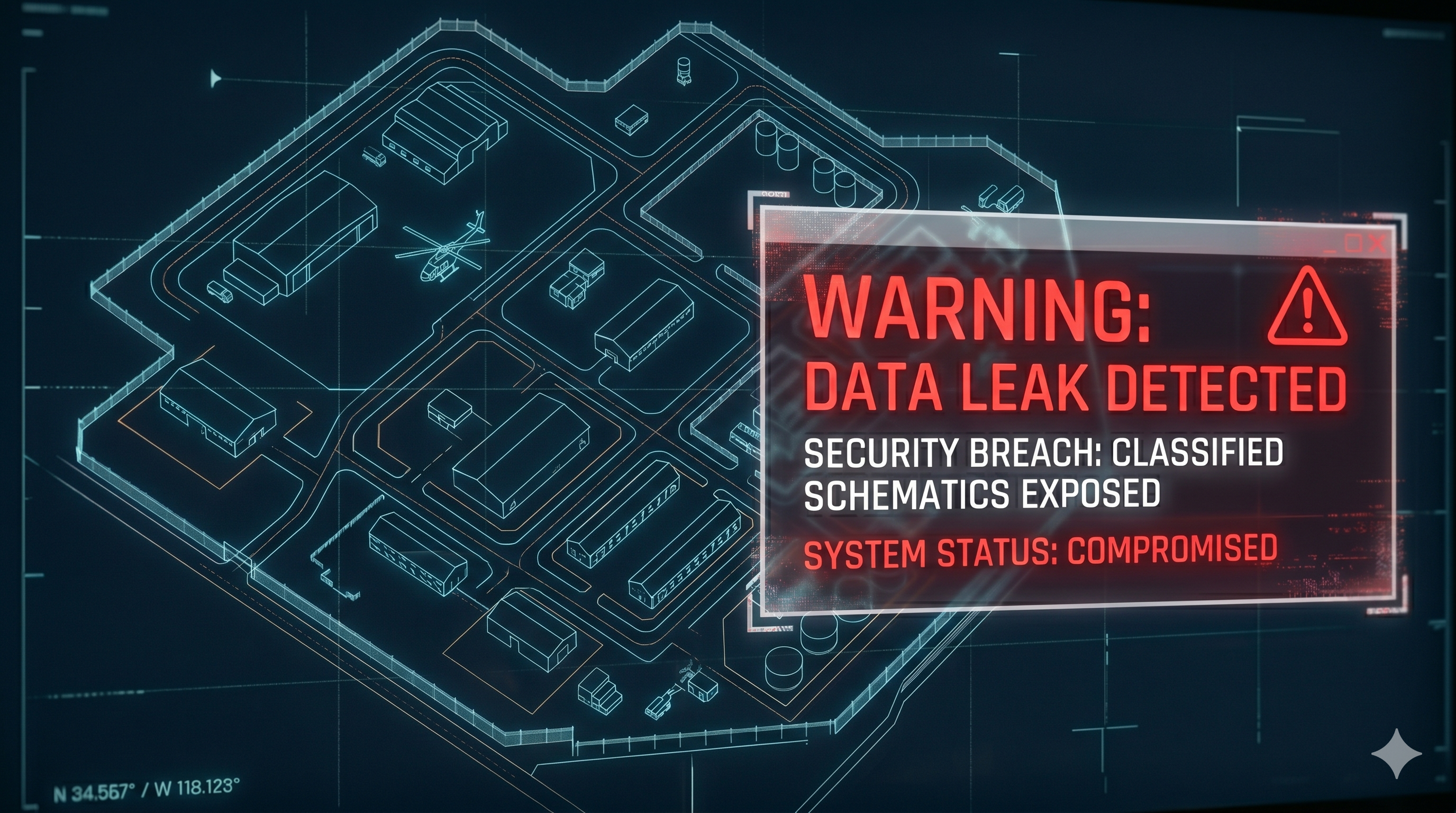
A leaky directory containing over 70,000 files relating to military personnel records, contractor records, and images taken inside military bases has been uncovered.
Researchers from Cybernews were tipped off about the leaky directory, and investigated the contents.
Despite the Cybersecurity and Infrastructure Security Agency (CISA) being informed by security researcher Arkadeep Roy in 2024, the dataset has remained exposed and was actively leaking as of April 2026.
Schematics and personnel files exposed
Cybernews discovered the dataset was being exposed via an Open Directory Listing Vulnerability. The directory also lacked sufficient security controls. The directory was found to belong to CMI Management Inc., a US government contractor, which is part of Dexterra Group.
According to the CMI Management website, the company specializes in providing government facilities services. The website states, “Over the years, CMI has successfully managed a wide range of government facilities, from training centers to mission-critical operations.”
The files were originally discovered in 2024, with CISA being notified the same year. On 16 March 2026, Cybernews was tipped off about the exposed database and launched an investigation the following day. Cybernews confirmed the leaky directory and reported it to CMI Management and CISA on 18 March 2026.
Cybernews shared a number of example images which have been heavily redacted to censor private information. The images include maintenance forms, emails between staff, and photos of internal infrastructure. Cybernews alerted CMI Management to the leaky directory but did not immediately receive a response.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
The leak of sensitive personnel and contractor information could put current and former US military personnel at risk of phishing or impersonation attempts, or personnel details could be used in order to gain unauthorized access to military installations.
Of particular concern is the leak of internal photos of US military bases, and base schematics, which could be used by threat actors to create detailed maps of US military bases and identify weak points in both structure and security.
“The data leak is concerning, as sensitive US military data was stored insecurely for over a year, even after CISA was reportedly notified. This signifies that even when it comes to the military and their facilities, it is too common to find data being stored insecurely, and remediation efforts are not prioritized even after notifying the relevant authorities,” the Cybernews research team said.
Following the Stryker Corporation cyber attack, CISA issued an alert in March 2026 with guidance on how organizations should harden endpoint management system configurations to defend against malicious cyber activity.

Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds.

Benedict is a Senior Security Writer at TechRadar Pro, where he has specialized in covering the intersection of geopolitics, cyber-warfare, and business security.
Benedict provides detailed analysis on state-sponsored threat actors, APT groups, and the protection of critical national infrastructure, with his reporting bridging the gap between technical threat intelligence and B2B security strategy.
Benedict holds an MA (Distinction) in Security, Intelligence, and Diplomacy from the University of Buckingham Centre for Security and Intelligence Studies (BUCSIS), with his specialization providing him with a robust academic framework for deconstructing complex international conflicts and intelligence operations, and the ability to translate intricate security data into actionable insights.
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.

 Become a TechRadar Insider
Become a TechRadar Insider







