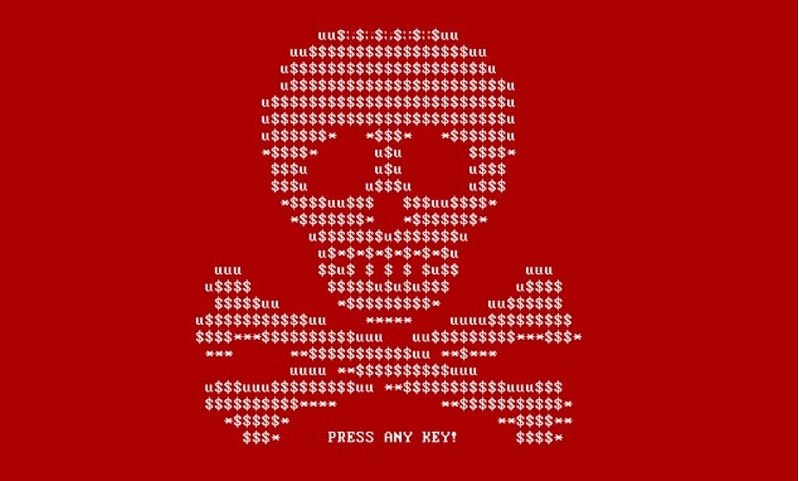
Windows PCs are being targeted with a nasty new malware - here's what you need to know
Hackers are using novel techniques to drop GHOSTPULSE on Windows PCs
Cybersecurity researchers have observed hackers abusing MSIX Windows app package files to distribute malware.
MSIX is a relatively new, unified packaging format, which developers can utilize to create secure and high-performing applications across platforms.
According to experts from Elastic Security Labs, someone’s been distributing MSIX files pretending to be popular software platforms such as Google Chrome, Microsoft Edge, Brave, Grammarly, and Cisco Webex. The distribution channels haven’t been confirmed, but researchers believe it’s the usual mix of compromised websites, SEO poisoning, malvertising, social media, and phishing.
Unknown motives
Being a loader, the malware itself has one job, and that is to drop one of the following final payloads: SectopRAT, Rhadamanthys, Vidar, Lumma, or NetSupport RAT. While these have different features, the common denominators are remote access, the ability to execute arbitrary code, and data exfiltration.
Users who fall for the scam and execute the file will see a prompt with an Install button. Pressing the button will drop the GHOSTPULSE malware loader onto their endpoint.
"MSIX requires access to purchased or stolen code signing certificates making them viable to groups of above-average resources," explained Elastic Security Labs researcher Joe Desimone.
Elastic Defend, the company’s endpoint security solution, detects this threat with the following behavior protection rules:
Are you a pro? Subscribe to our newsletter
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
DNS Query to Suspicious Top Level Domain
Library Load of a File Written by a Signed Binary Proxy
Suspicious API Call from an Unsigned DLL
Suspicious Memory Write to a Remote Process
Process Creation from Modified NTDLL
The YARA rule "Windows.Trojan.GhostPulse" will also detect GHOSTPULSE loaders on disk.
There is no information on the number of companies compromised with GHOSTPULSE, or who the threat actor behind the campaign is. We also don’t know what their end game is, but given the type of malware being distributed in the final stage, it’s safe to assume this is either a financially motivated group, or an Initial Access Broker (IAB).
An IAB will typically breach a network and then sell the access it has gained to other threat actors, such as ransomware groups.
More from TechRadar Pro
- Millions of Android phones are shipping with malware already installed
- Here's a list of the best firewalls today
- These are the best endpoint protection software right now
Sead is a seasoned freelance journalist based in Sarajevo, Bosnia and Herzegovina. He writes about IT (cloud, IoT, 5G, VPN) and cybersecurity (ransomware, data breaches, laws and regulations). In his career, spanning more than a decade, he’s written for numerous media outlets, including Al Jazeera Balkans. He’s also held several modules on content writing for Represent Communications.