Hackers abuse container technology to execute supply chain attacks
Malicious container images were hidden in plain sight on Docker Hub

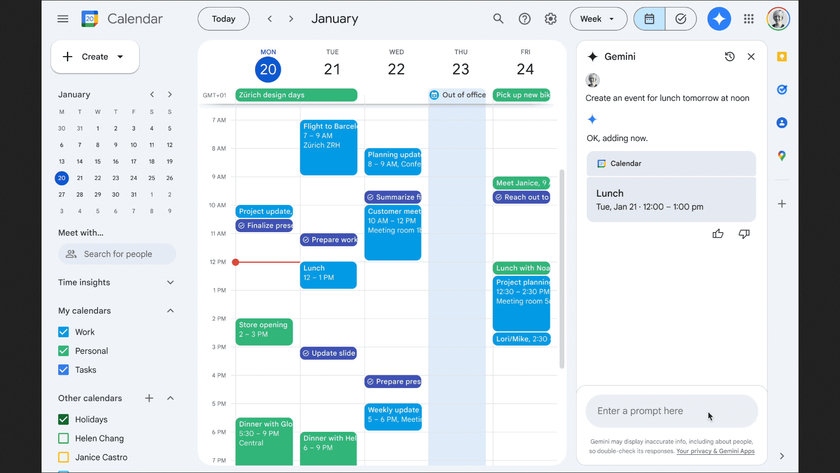
Cybercriminals have begun using malicious container images as a means to install cryptominers on enterprise networks though they can also be used as part of a supply chain attack targeting cloud native environments.
The cybersecurity firm Aqua Security uncovered several supply chain attacks that use malicious container images to compromise their victims when its threat research team, Team Nautilus was performing its daily scan of Docker Hub for malicious activity according to a new blog post.
The first three container images the research team discovered (thanhtudo, thieunutre and chanquaa) all execute a script called dao.py which is written in Python and was previously used in several campaigns that leveraged typo squatting to hide their malicious container images on Docker Hub.
- We've put together a list of the best cloud computing services
- These are the best endpoint protection software solutions
- Also check out our roundup of the best antivirus software
The dao.py script executes a binary called xmrig that is actually a Monero cryptocurrency miner hidden in one of the layers of the container image.
Malicious container images
Two of the container images (openjdk and golang) discovered by Aqua Security use misleading titles to appear as official container images from OpenJDK and Golang respectively.
The cybercriminals behind this campaign designed them in such a way that a busy user may accidentally mistake them as official container images despite the fact that their Docker Hub accounts are not official. After running these container images, the binary xmrig is executed which hijacks network resources for cryptocurrency mining.
Although the first two container images (thanhtudo and thieunutre) are likely intended to be used as part of a supply chain attack, the others are used primarily to mine cryptocurrency. Still though, all five malicious container images have gained over 120,000 pulls from Docker Hub.
Are you a pro? Subscribe to our newsletter
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
In order to protect your organization and its network from both cryptominers and supply chain attacks, Aqua Security recommends controlling access to public registries, scanning container images for malware using both static and dynamic analysis and digitally signing container images to maintain image integrity.
- We've also highlighted the best malware removal software
After working with the TechRadar Pro team for the last several years, Anthony is now the security and networking editor at Tom’s Guide where he covers everything from data breaches and ransomware gangs to the best way to cover your whole home or business with Wi-Fi. When not writing, you can find him tinkering with PCs and game consoles, managing cables and upgrading his smart home.